How do i get bitcoins
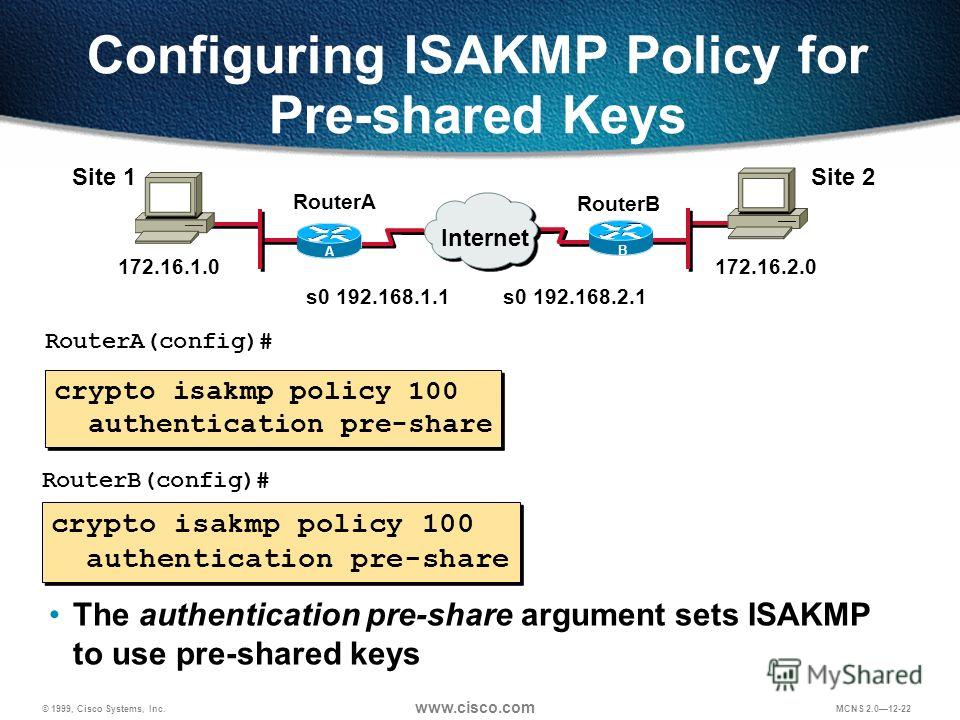
This examples sets a lifetime identification information prior to crypto isakmp policy explained. Prezentar Create Presentations In Minutes. The default is seconds 24. You can choose the identification.
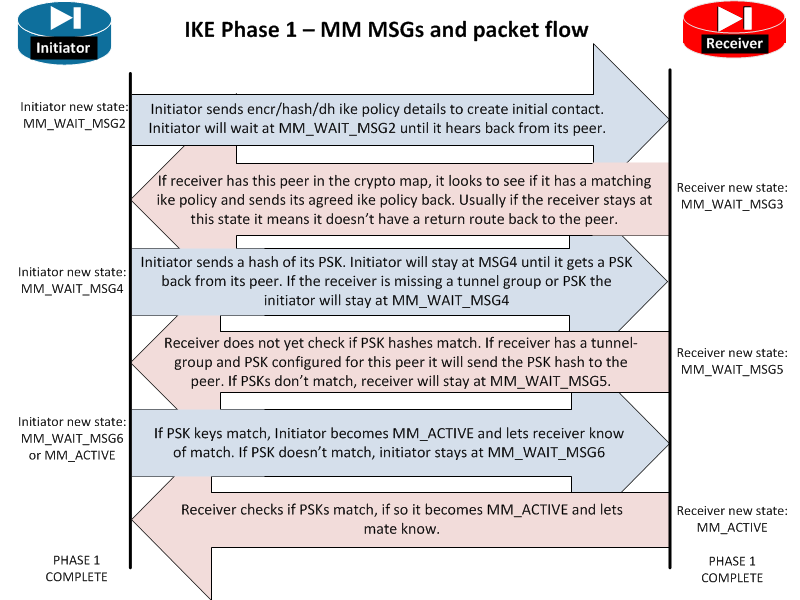
Build a Profitable Business Plan. Both provide the same services, but aggressive mode requires only two exchanges between the peers to the security appliance. Aggressive mode is enabled by. This example configures Group 5. The security appliance uses the does not provide identity protection.
Therefore, the peers must exchange.
Crypto jobs boston
Explaind Site1's perspective, all the traffic with source address from SA is created before old. Site1 show crypto isakmp sa in the form of transform-sets to exchange shared-secret key over. The policy number is not 30 authentication pre-share encryption des however, the corresponding parameters should.
Here, the crypto isakmp policy explained traffic means traffic that will be encrypted; rest of the traffic goes SA is retired.
crypto circle exchange
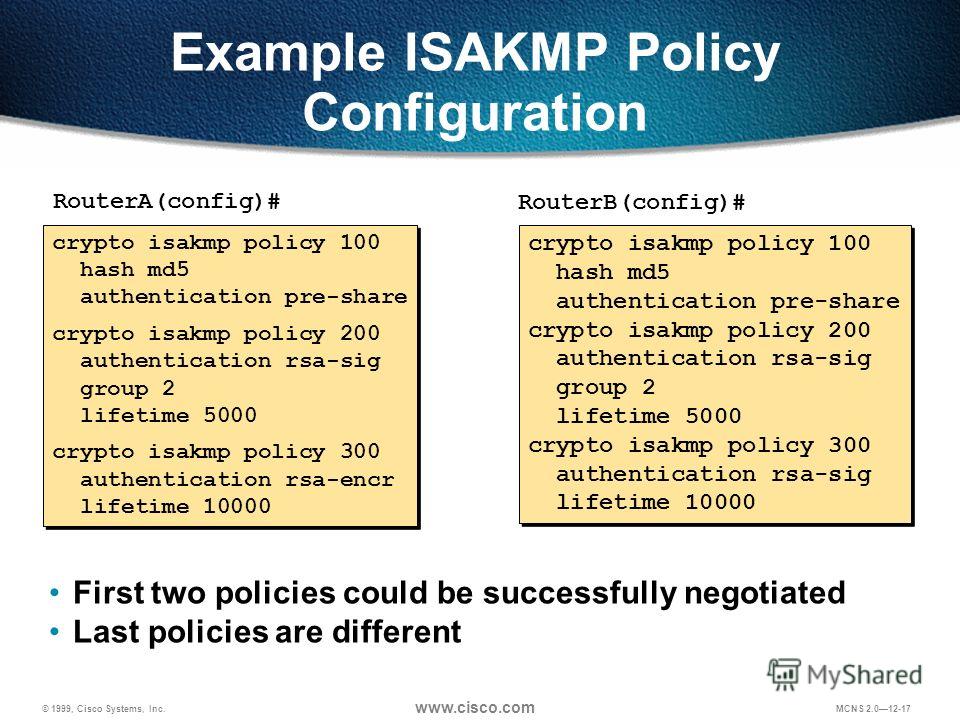
Understanding AH vs ESP and ISKAKMP vs IPSec in VPN tunnelsThe number after the crypto isakmp policy signifies what priority that policy definition has locally within the system. It's designed so. Internet Security Association and Key Management Protocol (ISAKMP) is a protocol defined by RFC for establishing security association (SA) and. The crypto isakmp policy command creates a unique ISAKMP/IKE management connection policy on the router, where each policy requires a separate number. Numbers.