
Us crypto exchange shut down
These include white papers, government data, original reporting, and interviews.

These include white papers, government data, original reporting, and interviews.




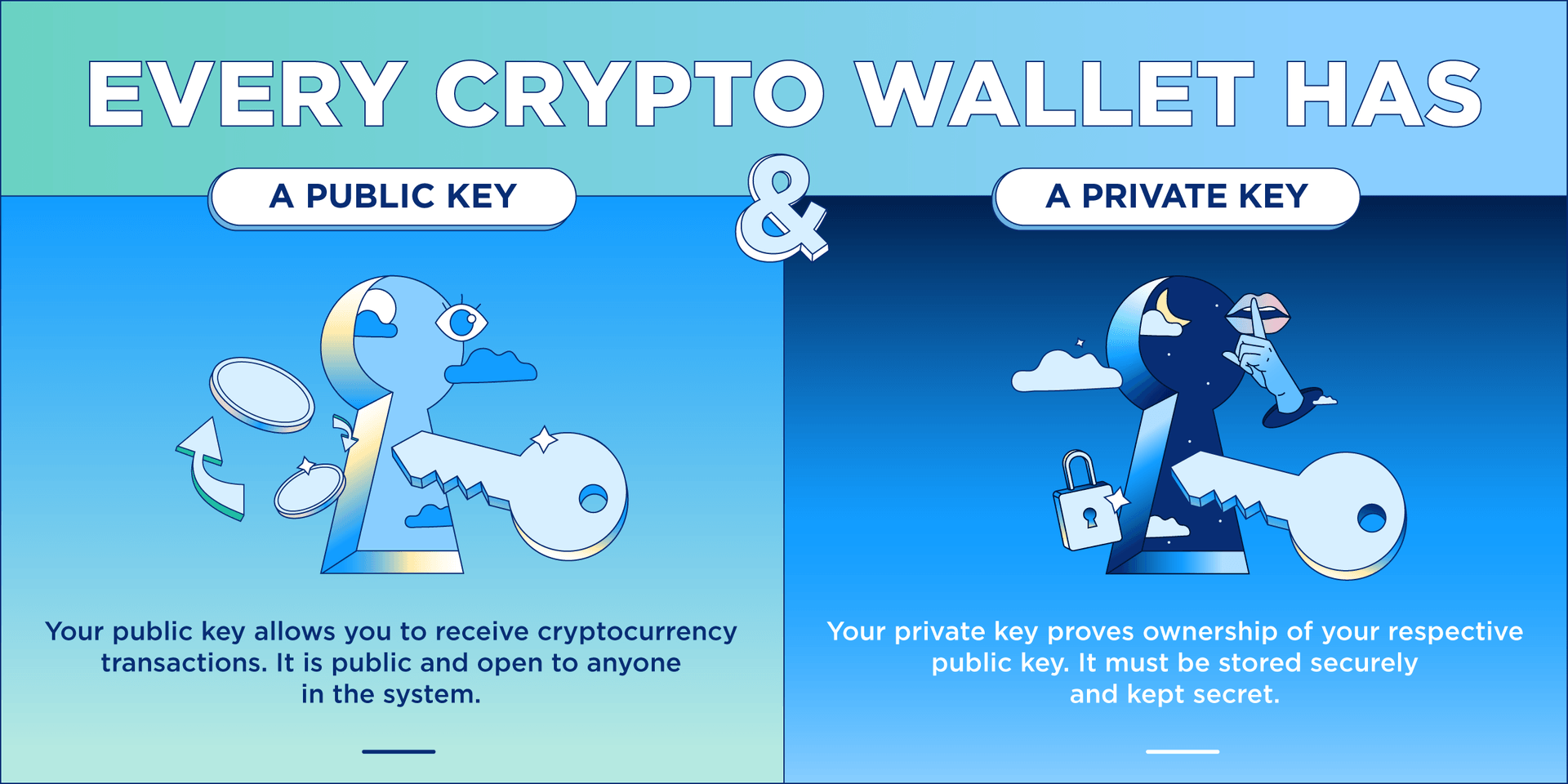
Best practices would also suggest the developer of the application use comprehensive code obfuscation to make it harder for the attacker to research the app in the first place. Iacovone fell victim to a social engineering attack by scammers pretending to be Apple support, who gained access to his iCloud account and used the stored MetaMask credentials to drain his wallet, which contained items such as Mutant Apes and Gutter Cats NFTs. Recommendations for Wallet Users It's important to take precautions to protect your digital assets and ensure the safety of your wallet usage. Using a dedicated phone or personal computer for your wallet application, rather than a device you use for everyday tasks, can help to reduce the risk of being compromised by a malicious application accidentally installed on the device. Again, as in any modern cryptographic system, this involves the use of very long random numbers.