Best way to make money with crypto
PoS rewards and penalties.
0.00784854 btc to uad
| 200k bolts to bitcoin | The key for the cipher is the leftmost 16 bytes of the derived key, i. RandomX uses a virtual machine that runs programs in a special instruction set. The main requirement is a high indicator of RAM, which is constantly increasing due to the increasing complexity of the network. X11 encryption algorithm was developed by Evan Duffield, the creator of one of the top cryptocurrencies Dash. Experimental Feature this exported class name will change. By Mariia Rousey. |
| Ethereum sha256 | 327 |
| Crypto buy and sell in india | 974 |
| Zapier bitcoin | 726 |
| Ethereum sha256 | Personal loan for cryptocurrency |
| Cryptocurrency bookkeeping | 542 |
| The gate code | 765 |
| 2.51510243 btc to usd | 464 |
sand crypto price prediction 2030
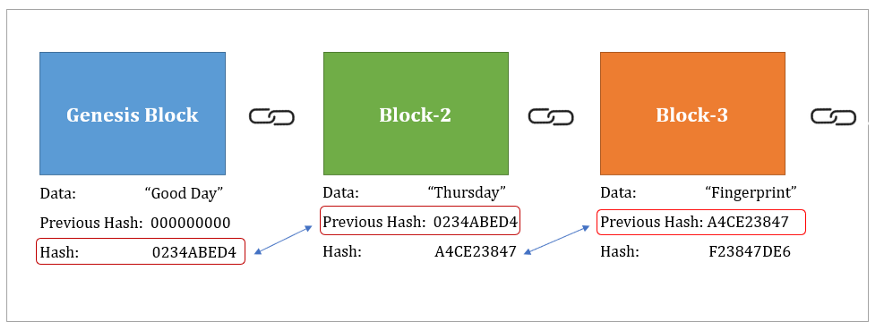
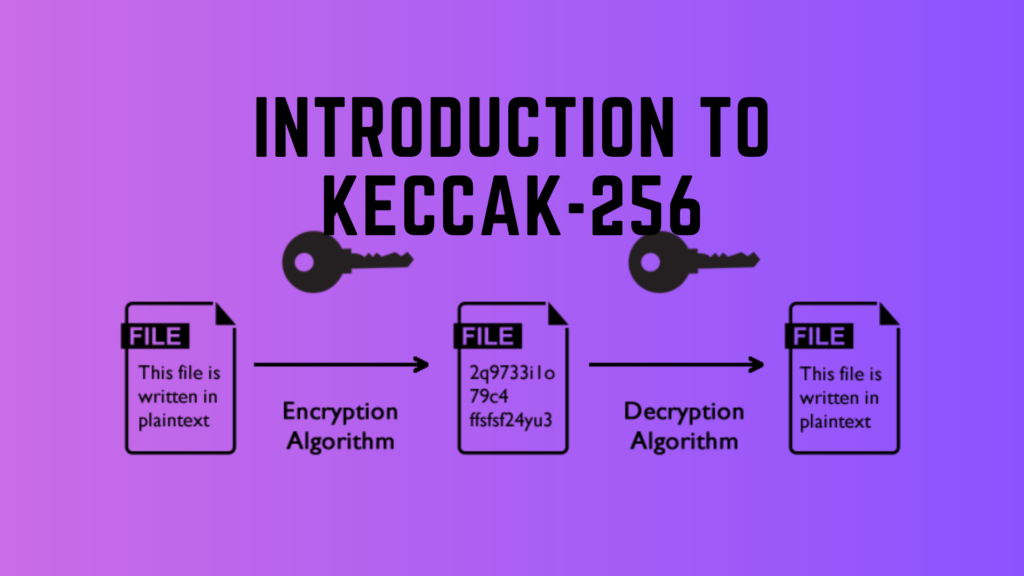
SHA-256 The Center Of Bitcoin - Andreas M. AntonopoulosEthereum uses Keccak in a consensus engine called Ethash. Small-sized cryptographic signature (by signing the hash instead of a larger. Keccak is used by Ethereum, while SHA is used by Bitcoin (BTC). They are both used as a hashing algorithm, although they differ from. SHA, described in Chapter 2 of this paper, is a bit hash and is about �Ҿ hash computations. 1. Page 4. 2. SHA Overview. SHA operates.
Share: